PVS-Studio 7.00
 Today is an important day — after 28 releases of the sixth version we present our PVS-Studio 7.00, in which the key innovation is the support of the Java language. However, during 2018 we have acquired many other important changes related to C++, C#, infrastructure and support of coding standards. Therefore, we bring to your attention a note that sums up the major changes that have happened in PVS-Studio for the last time.
Today is an important day — after 28 releases of the sixth version we present our PVS-Studio 7.00, in which the key innovation is the support of the Java language. However, during 2018 we have acquired many other important changes related to C++, C#, infrastructure and support of coding standards. Therefore, we bring to your attention a note that sums up the major changes that have happened in PVS-Studio for the last time.
PVS-Studio is a tool designed to detect errors and potential vulnerabilities in the source code of programs, written in C, C++, C#, and Java. It works in Windows, Linux, and macOS environment.
An extensive collection of errors found in code during the checks of various open source projects clearly demonstrates the abilities of the analyzer.
We’ll start with a change due to which we decided to change the version number from 6.x to 7.x. It is the analyzer support of the Java language, which required long time of preparation.
Java
The most important thing in the Java analyzer is that it appeared:). We’d like to invite Java developers to download the tool and check projects, on which you’re currently working.
We made available the most popular ways of the analyzer integration in the build system for the users:
- Plugin for Maven.
- Plugin for Gradle.
- Plugin for IntelliJ IDEA.
In case of using self-written build systems, we have the ability to run the analyzer directly, listing the sources and classpath.
You can find detailed information about all the ways how to run the analyzer on the documentation page «How to Run PVS-Studio Java».
We could not shy away from the SonarQube platform of the code quality control, which is so popular among Java developers, so we added support of the Java language in our plugin for SonarQube.
C, C++
In 2018, our team was actively working on the development of the C++ analyzer. Many new diagnostics appeared along with the algorithms, which allow collecting and processing the data extracted from the syntax tree.
CWE, CERT
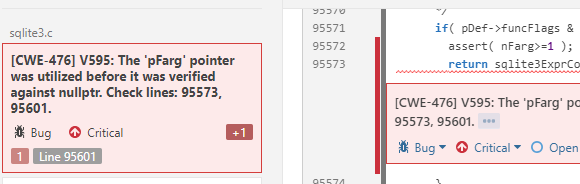
C++ (and C#) analyzer warnings were classified according to the Common Weakness Enumeration (CWE). CWE is a system of classifying potential and confirmed vulnerabilities. It is supported by the community with a view to identifying software problems and creating automated tools that can be used to identify and resolve these problems.
Additionally the messages were classified according to CERT C Coding Standard and CERT C++ Coding Standard. SEI CERT Coding Standards is a set of standards for writing software in C, C++, Java, and Perl, developed by the CERT (CERT Coordination Center, CERT/CC) to improve software reliability and security.
Classification of C and C++ diagnostics according to these warnings allows using PVS-Studio as a SAST solution.
MISRA
In 2018, a PVS-Studio static code analyzer has become able to classify its warnings according to MISRA C and MISRA C++ standards. Due to support of these standards, it has become possible to effectively use the analyzer to increase the level of security, portability, and reliability of programs for embedded systems.
Read more: «PVS-Studio: Support of MISRA C and MISRA C++ Coding Standards».
Support for MISRA has become relevant in connection with the development of various embedded systems support, which will be discussed in the next section of this article.
Embedded Development
In 2018, the following embedded compilers have been supported in PVS-Studio:
- Windows. IAR Embedded Workbench, C/C++ Compiler for ARM C, C++
- Windows/Linux. Keil µVision, DS-MDK, ARM Compiler 5/6 C, C++
- Windows/Linux. Texas Instruments Code Composer Studio, ARM Code Generation Tools C, C++
- Windows/Linux/macOS. GNU Arm Embedded Toolchain, Arm Embedded GCC compiler, C, C++
Two notes on the topic of supporting embedded systems:
- Static Code Analyzer PVS-Studio 6.22 Now Supports ARM Compilers (Keil, IAR).
- PVS-Studio Now Supports GNU Arm Embedded Toolchain.
Extending custom annotations
Sometimes such customized implementations of various system functions, as, for example, memcpy, malloc and so on are used in projects. The analyzer can detect errors in code which uses standard functions just fine, but in a customized code, it has been impossible to apply such algorithms until recently. Now using the annotation V_FUNC_ALIAS you can enter the names of your functions in compliance with the system ones.
Comment format:
//V_FUNC_ALIAS, implementation:sysf, function:f, namespace:ns, class:c
- Implementation key — specifies the name of the standard function to determine the alias.
- Function key — specifies the name of the alias. The signature of the function, the name of which is specified in this key, must match the signature of the function, specified in the implementation key.
- Class key is the name of the class. Might be missing.
- Namespace key is the name of the namespace. Might be missing.
Let’s look at an example:
//V_FUNC_ALIAS, implementation:memcpy, function:MyMemCpy
Now the analyzer will handle calls of the MyMemCpy function in the same way as calls of memcpy. For example, for such code a V512 warning will be issued:
int buf[] = { 1, 2, 3, 4 };
int out[2];
MyMemCpy (out, buf, 4 * sizeof(int)); // Warning!
C#
This year there were no significant changes of the C# analyzer. There were some improvements of diagnostics and errors fixes. Warnings of the C# analyzer, as well as warnings of the C++ analyzer have been classified according to the Common Weakness Enumeration (CWE). Mapping of C# diagnostics with the CWE identifiers is given here (see diagnostics with the numbers 3xxx).
We’re planning to return to more active development of the C# analyzer in 2019. We’re also planning to develop new diagnostics and improve the Data-Flow Analysis mechanism.
Report Converters
PlogConverter.exe and plog-converter utilities are included in PVS-Studio distributions for Windows and Linux/macOS, respectively. In addition, the source code of these utilities is available on GitHub.
With the advent of PVS-Studio for Java we have redesigned the code highlighting for C, C++, C# and have added Java in the FullHtml format (for a web-browser).
In addition, the MISRA column was added for the report in this format.
As well as CWE ID, the MISRA column is optional and is enabled by reviewers of code security when investigating the analysis results.
SonarQube Plugins
1. Full update
We’ve rewritten our plugins using the new API. This allowed us to add new features and provide compatibility with SonarQube 7 x. The minimum supported version is now SonarQube 6.7 LTS.
2. PVS-Studio for Java
The new version includes the support of diagnostics in the Java language. Now you can add PVS-Studio to other quality control tools of your Java project.
3. MISRA Standard
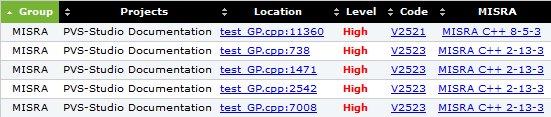
We have recently announced the support of MICRA C and MISRA C++ standards. New plugins also include their support. For example, the following parameter was added (in addition to CWE):
sonar.pvs-studio.misra=active
which includes adding of the MISRA identifier to the analyzer warnings:
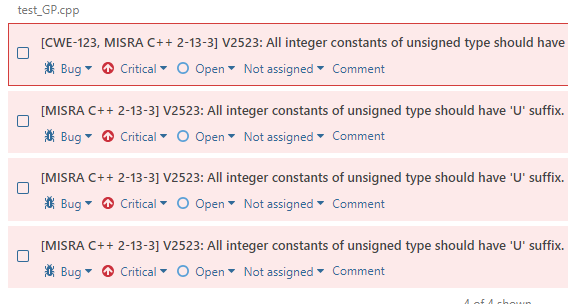
Regardless of this parameter, the search by tags misra and pvs-studio#misra will be available in the analysis results. Information on the number of the found MISRA warnings was added in metrics as well, which will be discussed next.
4. New metrics
In the menu Projects → Your Project → Measures, different code metrics are available, among which there is now various information from PVS-Studio:
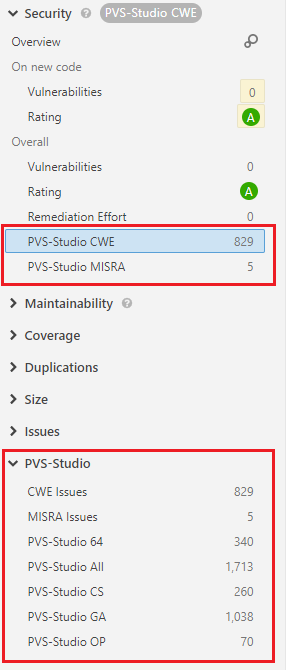
Using each of the metrics, you can build charts and monitor the dynamics of occurrence of various groups of warnings.
4. Multiline transitions
Some analyzer diagnostics issue warnings for several lines of code. Sometimes they are very far apart. In the new version, we added multiline transitions:
SonarQube also supports transitions between different files. Later we will add such transitions for diagnostics, in which there is an intermodular analysis.
6. Documentation
Documentation has undergone big changes. PVS-Studio is a cross-platform and multilingual product, therefore all processings have been focused on writing more common and easy-to-understand instructions for working on different systems.
SAST
Until recently, in our articles we have positioned PVS-Studio as a tool for detecting errors in code. While we have almost never regarded PVS-Studio in a security context. This year we remedied this situation and considered the tool in terms of testing of security applications and DevSecOps practices.
PVS-Studio is a static application security testing tool (SAST). In other words, the PVS-Studio analyzer detects not only typos, dead code and other errors, but also potential vulnerabilities.
For the convenience of specialists who will use PVS-Studio as a SAST tool, the analyzer can generate warnings in the following formats: Common Weakness Enumeration, SEI CERT Coding Standards. Mapping tables of PVS-Studio diagnostics to different standards:
- CWE mapping
- SEI CERT mapping
This topic was described in more detail in the article «PVS-Studio as SAST solution».
We also suggest viewing these publications:
- How Can PVS-Studio Help in the Detection of Vulnerabilities?
- Shoot yourself in the foot when handling input data.
- Handing out PVS-Studio Analyzer Licenses to Security Experts.
PVS-Studio Free
On the New 2019 year’s eve, a PVS-Studio team decided to make a nice gift for all contributors of open-source projects hosted on GitHub or Bitbucket. They are given free usage of PVS-Studio static analyzer for development of open source projects.
Details: «Free PVS-Studio for those who develops open source projects».
macOS
In 2018, PVS-Studio has started to work under macOS. Our team decided perform a XNU Kernel check to coincide it with this event: «PVS-Studio is now available on macOS: 64 weaknesses in the Apple’s XNU Kernel».
XNU is a kernel of computer operating systems developed by Apple and used in OS X operating systems (macOS, iOS, tvOS, watchOS).
