How to prevent targeted cyber attacks? 10 best network sandboxes

Targeted attacks are the most dangerous among the multitude of modern cyber threats. They are also known as ATP (an abbreviation which stands for Advanced Persistent Threat). Those are not viruses that can accidentally get into the computer due to user’s carelessness. Neither it is an attempt to replace the address of a popular site in order to cheat billing information from credulous users. Targeted cyber attacks are prepared and thought out carefully and pose a particular threat.
The target of an attacker could be both a number of organizations (for example, government agencies) and industries and some specific company. IT professionals are well aware that this kind of attacks can easily bypass traditional means of protection. One of the main tools for dealing with them is network sandboxes. In our review, you will find information about the most advanced sandboxes in the market and will be able to choose the most suitable for you in terms of parameters in the special Sandbox comparison table

What is a sandbox? In broad terms, it is an isolated secure environment that simulates an operating system with all its components — drivers, settings, common software, etc. In the sandbox, you can run suspicious files and programs to monitor their behavior and understand their purpose without endangering organization network and endpoints. By and large, it would be more correct calling the technology differently — a «cell» or an «isolator» because those names would clearly convey the meaning and purpose of the medium. But we have what we have.
Why are sandboxes that relevant? When conducting targeted attacks, cybercriminals often use so-called zero-day threats. Those are viruses and exploits that have just come into being (or were written specifically for a particular attack) and have not yet been entered into the signature databases of traditional defense tools. Yes, the databases are updated very often, but sometimes several hours are enough to cause significant damage. Also, some malware can remain undetected for months due to their behavior. Sandboxes, on the other hand, allow you to detect malicious actions in a safe environment, where a malicious program can make a try to harm as much as it is possible without any result though. Of course, sandboxes themselves are not a panacea for zero-day threats and targeted cyber attacks. When attacks are carried out, the whole arsenal of tools available to attackers is used. So this is rather an important element in the information security system of every organization. Without it, any built protection can hardly be called reliable.
Sandboxes can work both as a separate hardware solution and as a virtual or cloud service (a combination of these methods is also used). At the same time, it is considered that the most effective solution is hardware. Hardware solutions are supplied both as independent means and as a part of complex products to combat targeted attacks and other threats. Further, in our review we will consider solutions from leading IT companies that are popular in the market and reported by Gartner experts as reliable and proven solutions for information protection.
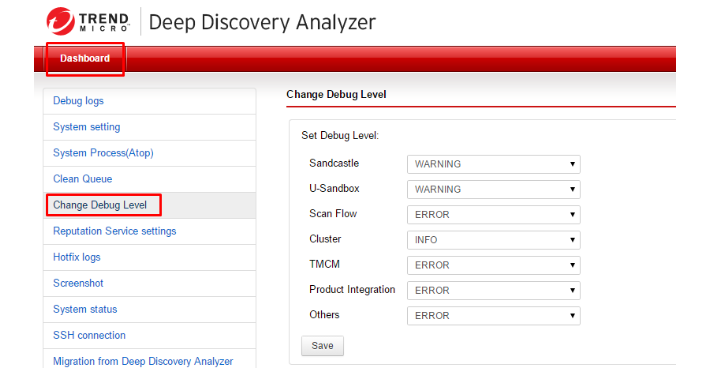
Trend Micro Deep Discovery

This product is a part of the integrated Trend Micro Deep Discovery system, which is designed to protect corporate networks from all common types of threats and can also be used independently. Deep Discovery analyzer uses virtual images, which completely replicate installed systems and their settings, including drivers, utilities, applications, and even language versions, like a sandbox. The module is able to check and analyze a variety of executable files, Microsoft Office and PDF documents. It also processes content of the viewed Internet pages as well as downloaded content from those pages (including multi-level downloads). At the same time, Deep Discovery analyzer can detect common vulnerabilities in office documents and malicious programs that use them. One of the most urgent functions today is detection of ransomware programs. The tool detects the following threats and attacks: zero-day threats, hidden execution of malicious scripts, mass file encryption and other actions typical for ransomware programs. For this purpose not only direct behavior analysis is used, but also a global reputation system, as well as a large list of behavioral patterns.
The solution allows you to deploy up to 60 sandboxes on one device and supports virtualization. Multiple Deep Discovery analyzer hardware devices can be clustered to increase productivity. It can also integrate with Trend Micro products and third-party protective equipment.
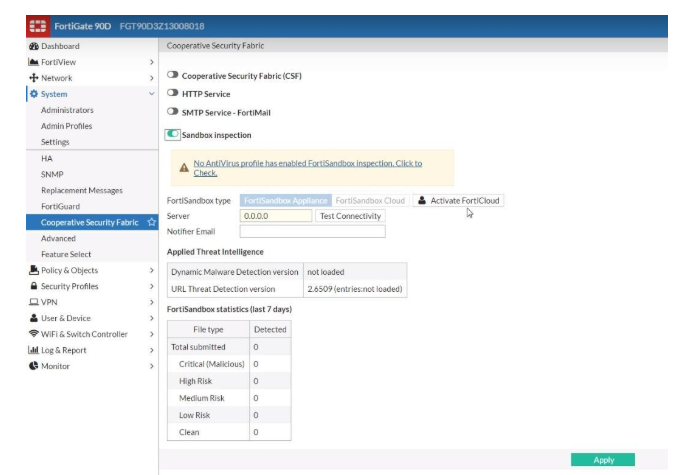
Fortinet FortiSandbox

Sandbox from Fortinet is an advanced emulation system for detecting unknown zero-day threats and targeted attacks using a wide range of tools. It uses virtual machines that emulate normal operating environments — operating systems with installed drivers and software. In this case, you can use standard virtual machines with pre-installed OS and programs (Adobe Flash Player, Java Run Time, etc.), but there is also an option to upload images of your own workstations. Scanning of suspicious objects in FortiSandbox is carried out in several stages. First, an ordinary antivirus scan takes place, then the object is scanned using the FortiGuard cloud service. And only if during these checks it is impossible to determine whether the object dangerous or safe, it is redirected for scanning in the sandbox. This procedure allows you to significantly save your resources because some of the files are checked without using the sandbox mechanism directly. This solution works with individual files and can also check web links.
Fortinet FortiSandbox is available both as separate devices (five models are available in total) and as a cloud service (supports public and private clouds). Also, the solution can function on the client’s equipment as a virtual machine. The tool integrates with other Fortinet products, for example, FortiGate and FortiWeb security tools. This allows you to improve the quality of verification, including an ability to work with encrypted traffic.
Forcepoint Advanced Malware Detection

This Forcepoint product can be used in all leading vendor solutions as a separate module. Among them: cloud services Cloud Access Security Broker, Web Security and Email Security, as well as proprietary hardware next-generation firewalls (NGFW). This module is activated by a separate subscription and can be suspended in the same way without affecting the operation of products as a whole.
The Forcepoint Advanced Malware Detection sandbox emulates not only the operating system, but the entire host, including the processor, RAM, and other components. At the same time, this embedded in-depth analysis tool keeps track of all the actions of the executed programs and can even detect inactive codes for verification. This allows you to detect hidden threats and scripts that usually run a few weeks or even months after infection, and did not show themselves previously. Besides, Advanced Malware Detection monitors suspicious actions, even if they are performed by the operating system or trusted programs. This approach allows you to deal with the specific class of threats that delegate malicious actions to other tools.

FireEye Malware Analysis

As a proprietary sandbox, FireEye offers a hardware solution — a device called Malware Analysis AX 5550. It allows you to run powerful, automatically customizable test environments based on Windows and MacOS. They track malware and zero-day threats that could get into the network through email attachments, regular files and malicious links. The device uses a proprietary Multi-Vector Virtual Execution engine which can track attacks from the initial execution of malicious code to the final stages when the script tries to download some missing components. All outbound connection attempts across multiple protocols are also monitored.
The platform allows you to work in two modes: directly in the sandbox and live. The last option is useful when there is a complex targeted attack. It allows real-time tracking of all vectors and attack stages in a secure environment. In addition, Malware Analysis exchanges information about attacks with other proprietary devices, so that information about new zero-day threats becomes available very quickly over the network. This, in turn, makes it possible to prepare in advance for such an attack and reduces its potential danger.

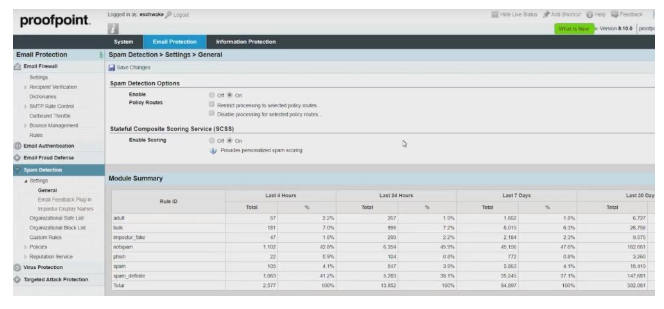
Proofpoint Targeted Attack Protection

Email is known as one of the most common methods of getting malware on computers. Proofpoint has developed Proofpoint Targeted Attack Protection product line which has an email protection tool along with others. It is a cloud service that uses cloud-based sandbox which scans email attachments and links to detect targeted attacks and zero-day threats. The tool scans mail traffic at all common types of devices, including mobile ones. It protects not only from malware but also from phishing links, which are also very often found in emails. At that point not only the mail itself is scanned, but also the behavior of the accounts is monitored, which allows detecting anomalous activity and blocking it. This feature is very useful if an email account has been hacked. The tool also analyses the number of attacks for each account and informs administrators which of them are the most attacked and makes it possible to work with specific people.
Proofpoint Targeted Attack Protection supports most email services, including Office 365 and private corporate services. The tool is quickly deployed and configured. It can be used both as a standalone solution and as a module of another company product — Proofpoint Protection Server.
Zscaler Cloud Sandbox

To protect against zero-day threats and targeted attacks Zscaler offers its own cloud-based sandbox. This tool can be used as a standalone solution, as well as a part of the Zscaler Web Security integrated product. One of the main advantages of Zscaler Cloud Sandbox is the ability to scan encrypted traffic and use machine learning to identify threats. Also, the product widely applies security policies that can be configured by administrators personally. For example, you can check files by type and also pay special attention to privileged users (supervisors, etc.). A properly configured security policy determines what to do with suspicious files — block them, quarantine them, or simply notify users.
Since the analysis of files takes place inside the cloud, Zscaler Cloud Sandbox works very quickly, and leading to the company’s infrastructure is minimal. It also allows you to protect users' devices regardless of their location, such as office notebooks and employees' smartphones on business trips and outside the office.

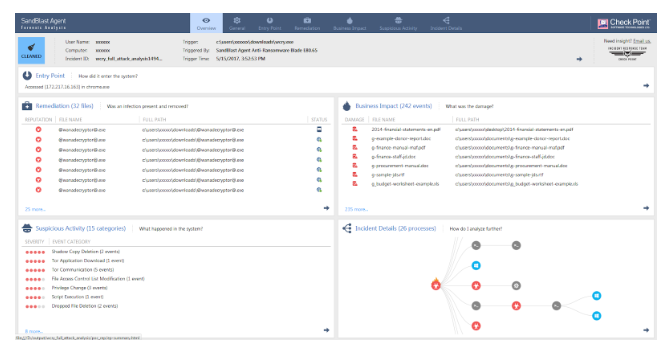
Check Point SandBlast

Sandbox from Check Point is a technology that is used in a number of branded tools. Thes include: SandBlast Network Security for Next-Generation Firewalls (NGFW), SandBlast Agent, which protects endpoints, and SandBlast Cloud, which works with Office 365 cloud service and protects corporate e-mail. The product can analyse more than forty types of files and dangerous content from them, which allows using the files without any harm. SandBlast protects against both known viruses and zero-day threats. The product analyses execution of files at the level of the processor instructions and the system core, which prevents the very possibility of launching infected objects. This, in turn, saves resources for verification and allows you to quickly process requests.
SandBlast actively uses the Check Point ThreatCloud system, a global database of threats identified by Check Point itself, in its work. The signatures of new threats appear in it immediately after detection and are promptly delivered to all devices connected to the system. This makes it possible to respond very quickly to zero-day threats, which are not yet present in traditional anti-virus databases, and which are also used in SandBlast.
Palo Alto Networks WildFire

The comprehensive product from a reputable developer of protection and control and network traffic. Sandbox WildFire can analyze all common file types, and also supports work with encrypted traffic. A combined approach is used to identify zero-day threats, targeted attacks, and other malicious objects. For example, in addition to dynamic and static analysis in the sandbox, anti-virus, hidden tunnel signatures, machine learning, and information from other Palo Alto Networks devices around the world are used. Analysis of potential threats in WildFire occurs both on local servers and virtual machines, as well as in the developer’s cloud. This helps to bypass some tricks of intruders. For example, there is a dodge technology. It allows a malicious object to determine that it is being tested on a virtual machine and not to show itself (evade). The ability to test on real equipment eliminates such tricks. When the platform determines that the object is evading the check, it sends it to the real sandbox server for verification.
Palo Alto Networks WildFire has a proprietary technology called TRAPS, which is used as an endpoint protection. It monitors traffic in real time and as soon as it detects execution of malicious code using one of the known vulnerabilities it creates a virtual trap for the code, which closes the executed malicious process.

McAfee Advanced Threat Defense

The American company McAfee is positioning its Advanced Threat Defense product as a comprehensive solution to combat complex targeted attacks and zero-day threats. McAfee Advanced Threat Defense comes both as a locally deployable hardware (there are two models of devices) and in a virtual form. Besides that, private and public cloud environments are supported. Among all the tools used in this platform, there is a proprietary sandbox. Potentially dangerous objects are subjected to dynamic analysis when launched in a protected environment inside it. In addition to the behavioral analysis, the tool also uses a signature analysis and machine learning system, verifies the reputation of objects. McAfee Advanced Threat Defense allows you to customize images of the systems for analysis, which increases the reliability of work, the accuracy of threat detection and the speed of investigation. The interactive user mode allows administrators to independently study malware samples, while a large set of unpacking features significantly reduces time for investigating incidents.
McAfee Advanced Threat Defense seamlessly integrates with other security devices located on the corporate network. This applies not only to McAfee branded solutions, but also to third-party products. Thus, these devices can make decisions about threats as soon as Advanced Threat Defense determines them. This feature allows you to respond to threats really quickly and not to waste resources on rescanning files if they have already been recognized as malicious. Product integration can occur either directly or with special connectors, for example, McAfee Threat Intelligence Exchange or McAfee Advanced Threat Defense Email Connector.

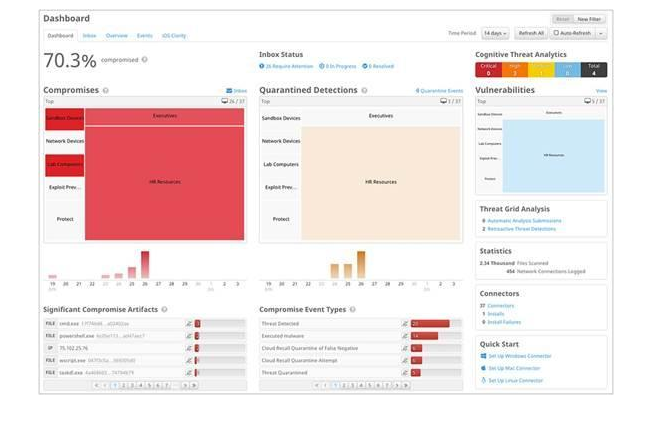
Cisco Advanced Malware Protection

This solution is a comprehensive system to protect against advanced attacks and zero-day threats. The platform consists of several components designed to perform different tasks. For example, Advanced Malware Protection for Networks protects corporate networks, Advanced Malware Protection for Endpoints works with endpoints (including mobile devices), and Advanced Malware Protection for Content scans web traffic and email. But all these modules use a proprietary Cisco sandbox, which can perform static and dynamic analysis of objects, and uses more than 700 behavioural indicators to detect malicious code.
Threat detection in Cisco Advanced Malware Protection is accomplished by using a combination of different methods. In addition to the behavioral analysis, signature tests, heuristics and machine learning are used. The system checks files not only at its entrance point, but also monitors their behaviour over the period they stay in the corporate network, regardless of their location. This helps to quickly detect a threat that has been inactive for a long time and began its harmful activity only weeks or months later. The same mechanism applies to threats, which harmfulness traced only using a long observation.
Small afterword
Network sandboxes are quite diverse, but they pursue one goal — protect the network and endpoints from attacks that cannot be recognized by traditional methods. This is an important part of the corporate information security system, and without it you cannot to be a 100% sure that your infrastructure is protected. There are enough solutions in the market, both hardware and cloud, that can cope with the task. Our Sandboxes comparison table will help you choose the best option.
Author: Vladyslav Myronovych, for ROI4CIO
